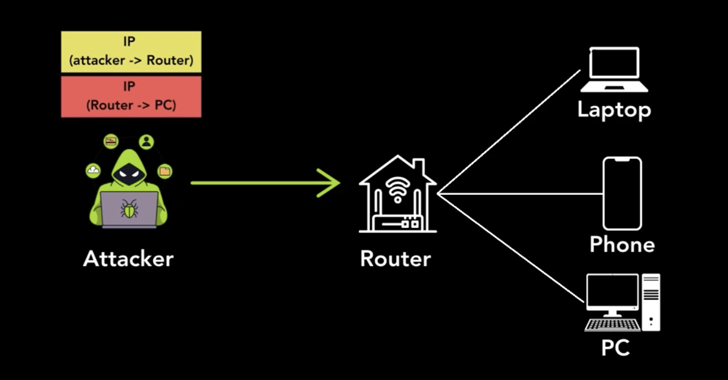
New research has uncovered security vulnerabilities in multiple tunneling protocols that could allow attackers to perform a wide range of attacks.
“Internet hosts that accept tunneling packets without verifying the sender’s identity can be hijacked to perform anonymous attacks and provide access to their networks,” Top10VPN said in a study, as part of a collaboration with KU Leuven professor

Unsecured Tunneling Protocols Expose 4.2 Million Hosts, Including VPNs and Routers
 Xander.Ritt@gmail.com
Xander.Ritt@gmail.com Valdosta, GA
Valdosta, GA
Leave a Reply